in the context of increasingly stringent cross-border and compliance requirements, enterprise-level deployment of hong kong station cluster interface permission classification and audit tracking have become the key to ensuring business continuity and security compliance. this article focuses on design principles, permission models, authentication and authorization, and audit links to provide practical implementation methods and operation and maintenance suggestions, which is suitable for reference by security, development, and operation and maintenance teams.
design principles and goals
permission classification and audit tracking should follow the four principles of least privilege, auditability, traceability and recoverability. the goal is to achieve controllability and event traceability of access to hong kong station group interfaces through hierarchical authorization, centralized policies and fine-grained logs, meet security audit and supervision requirements, and ensure business performance and convenient operation and maintenance.
permission classification model selection
for hong kong site groups, common permission models include role-based permission control (rbac) and attribute-based permission control (abac). rbac is suitable for scenarios with clear team and position structures, while abac supports more flexible strategy combinations. it is recommended to use a hybrid model of rbac+attribute conditions based on business complexity.
role and least privilege policy implementation
in actual deployment, interfaces and business boundaries should be sorted out first, basic roles and responsibilities matrix should be defined, and then access rights should be gradually granted based on the principle of least privilege. in order to avoid permission expansion, establish a regular permission review and approval process, and incorporate role management into iam or a unified permission platform for unified maintenance.
interface authentication and authorization process
interface access should first pass strong authentication (such as oauth2.0, jwt or mtls), and then perform fine-grained authorization judgment. it is recommended to bind subject identification and context information during the authentication phase, and use a policy engine (such as opa) to evaluate roles, attributes, and environmental conditions during the authorization phase to ensure that permission decisions are unified and auditable.
api gateway and strategy sinking
the api gateway is the first line of defense for permissions and auditing, and should implement unified authentication entrances, rate limits, black and white lists, and policy distribution. execute general policies on the gateway side, and push complex policies to microservices or policy engines, ensuring both performance and policy consistency and centralized management and control capabilities.
audit trail system design
the audit system needs to cover key fields such as request metadata, identity context, policy decisions and execution results, and generate structured logs. a unified audit field format should be designed to facilitate subsequent aggregation, indexing and quick retrieval, ensuring that each interface call can be traced back to the source and analyzed behavior.
log collection and link tracking
auditing from a cross-service perspective can be achieved by adopting a centralized logging platform (elk/efk or a cloud-native alternative) combined with distributed link tracing (such as opentelemetry). to ensure log integrity, reliable transmission and long-term storage strategy, sensitive fields should be desensitized or encrypted.
alert, detection and compliance reports
the audit system should support real-time anomaly detection and rule-based alarms (such as unauthorized calls, abnormal frequency or ip anomalies). at the same time, compliance reports are regularly generated, including permission change records, audit results and event handling processes, to meet internal governance and external supervision requirements.
operation and maintenance, automation and rollback mechanism
the operation and maintenance level needs to implement grayscale and rollback mechanisms for policy release, and permission changes should be executed through the ci/cd pipeline and automated approval. establish a drill mechanism and fallback plan to ensure rapid recovery in the event of misconfiguration or anomalies, and retain audit evidence for post-analysis.
cross-border compliance and data sovereignty considerations
in the hong kong site cluster scenario, attention should be paid to compliance requirements such as data sovereignty, cross-border access control, and audit retention periods. classify sensitive data and clarify geographical restrictions and access review processes in permissions and audit policies to reduce compliance risks and regulatory exposure.
summary and suggestions
in summary, enterprise-level deployment of hong kong station group interface permission classification and audit tracking needs to be coordinated from five aspects: model design, authentication and authorization, gateway strategy, log link and operation and maintenance automation. it is recommended to implement a phased implementation plan first: define roles and strategies, build gateways and audit platforms, gradually implement strategies, and conduct regular reviews and drills to achieve a balance between security, compliance, and high business availability.

- Latest articles
- Newbie Configuration Guide Vps Server Access To The United States Port And Firewall Setting Tips
- Beginner's Guide To Quick Start Deployment And Frequently Asked Questions About Vietnam Cn2 Server
- How To Choose A Stable And Reliable 4-u.s. Site Group Server To Achieve Multi-site Management
- Hong Kong Site Group Server Post Template Examples And Content Layout Strategies Help Increase Rankings
- Analysis Of The Role Of Vietnam Server Native Ip In Video Distribution And Live Broadcast Acceleration
- Shuozhou Japanese Cloud Server Maintenance, Migration And Upgrade Risk Control And Compatibility Testing
- Mobile's Practical Guide To Multi-line Redundancy Deployment In Serverless Scenarios In Malaysia
- An In-depth Interpretation Of Which Hong Kong Vps Is Reliable After Comparing The Three Major Operators
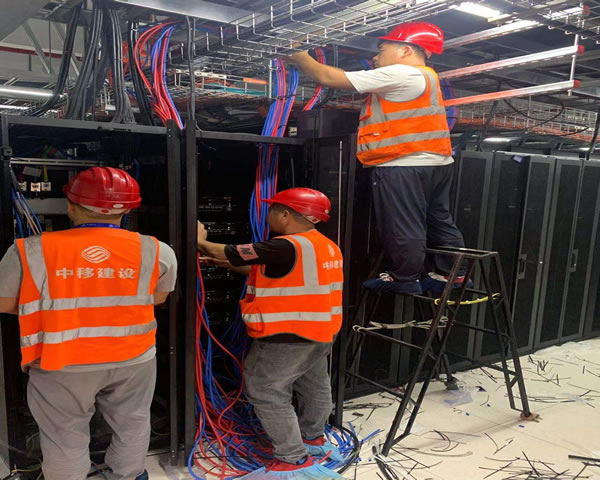
- Engineer Explains The Installation Details And Maintenance Methods In The Picture Of Hong Kong Computer Room Blower
- The Effect And Scheduling Suggestions Of Malaysian Cn2 In Cross-border E-commerce Peak Traffic Management
- Popular tags
-
Legality Of Using Hong Kong Native Ip Tvb And Service Provider Compliance Guide
this article analyzes the key points of legality judgment and service provider compliance inspection when using hong kong native ip to access tvb, provides practical suggestions on privacy, security and legal risks to help users reduce compliance risks. -
Hong Kong App Server Selection And Advantages Suitable For Mobile Applications
this article explores the selection and advantages of hong kong app servers suitable for mobile applications to help developers find the best solution. -
Detailed Technical Explanation Of What Hong Kong’s Native Ip Means And Suggestions For Using Hong Kong Vps
this article provides a detailed technical explanation of "what does hong kong native ip mean and suggestions for the use of hong kong vps", providing executable optimization suggestions from definitions, technical principles, advantages and application scenarios to deployment and security compliance.